Foundational Security
Essential protection for devices, email, and networks through continuous monitoring, secure updates, and managed endpoint controls
Advanced Security
Incident response, penetration testing, and vCISO guidance to strengthen defences and manage complex cyber threats
Microsoft 365 Security
Configuration, access, and monitoring controls that protect Microsoft 365 accounts, files, and sensitive business data
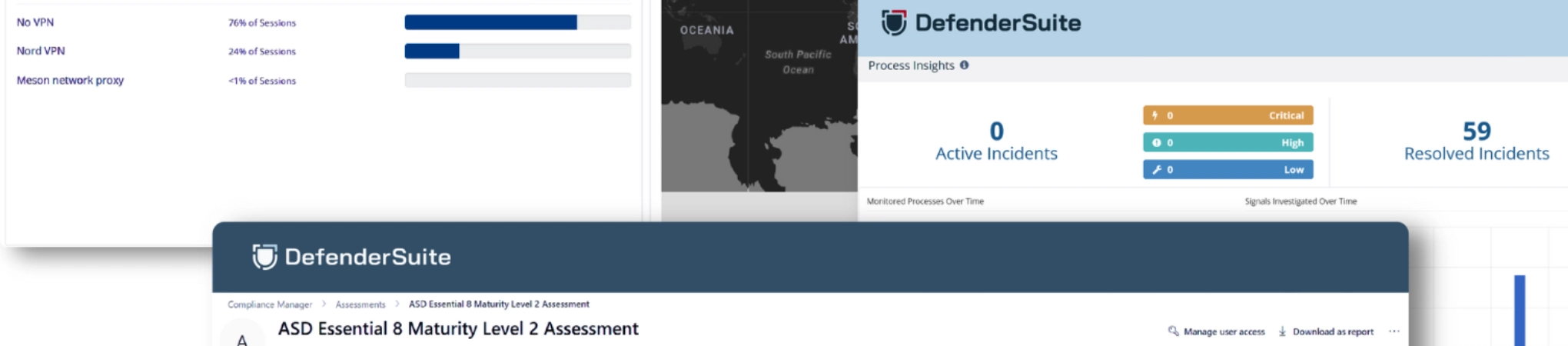
Compliance Governance
Policy frameworks, audit preparation, and reporting that demonstrate alignment with recognised Australian cybersecurity standards
Insurance Readiness
Security reporting and evidence tracking to support insurer reviews and meet client and policyholder expectations
View the framework that guides DefenderSuite’s security and compliance solutions
Baselines & Maturity Models
Cyber Security Act
Align security practices with national law and reporting duties
Essential Eight
Reach and maintain required Essential Eight maturity levels
SMB1001 Alignment
Benchmark cybersecurity maturity and resilience for SMBs
Platform & Technical Guidance
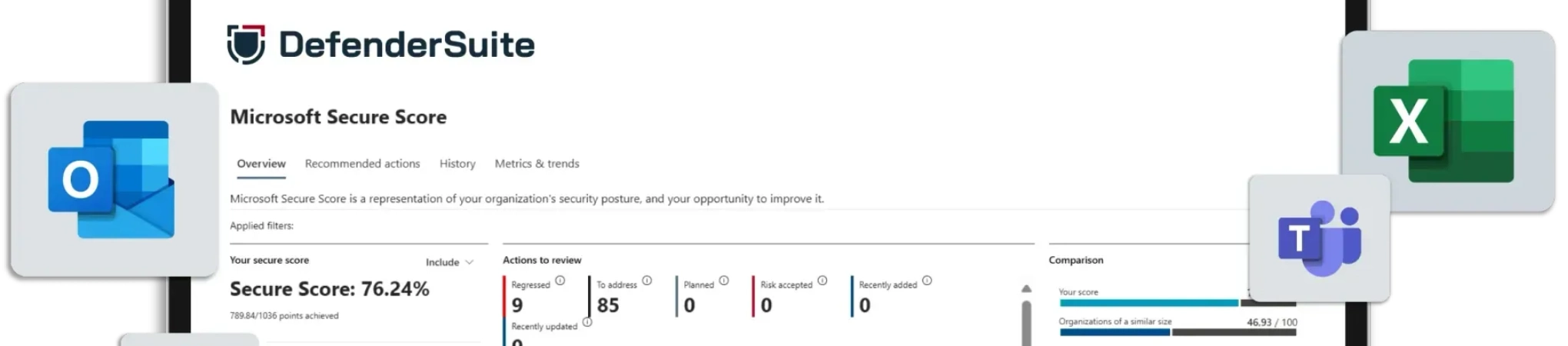
Microsoft Secure Score
Improve Microsoft 365 protection and Secure Score performance
Australian Signals Directorate Hardening Guidelines
Control data access and prevent unauthorised change
Australian Signals Directorate Blueprint for Secure Cloud
Secure Microsoft 365 and Azure with ASD cloud guidance
Government & Defence Assurance
Information Security Manual
Safeguard sensitive data and manage risk under ISM controls
Protective Security Policy Framework
Apply PSPF principles to protect people, data, and assets
Information Security Registered Assessors Program
Prepare systems for ASD-accredited IRAP security assessments
Defence Industry Security Program
Align controls for Defence supplier assurance and membership readiness
View the framework that guides DefenderSuite’s security and compliance solutions
Regulated & Compliance-Driven Sectors
Finance Firms
Protect client data with identity hardening and Microsoft 365 security
Legal Practices
Protect confidential matters with managed access and continuous monitoring
Healthcare
Protect sensitive records with controlled access and managed device security
Defence Partners
Apply structured controls, monitoring, and uplift for Defence-ready security
Data-Centric & Client-Focused Services
Technology & SaaS
Support secure operations with identity hardening and continuous monitoring
Consulting & Advisory
Protect client work with managed access, device protection, and controlled sharing
Recruitment & HR
Protect candidate data with identity controls and secure cloud access
Operational & Project-Based Industries
Engineering & Design
Protect design files and project systems with managed identity and monitoring
Real Estate & Property
Protect contracts and client files with managed access and monitoring
Logistics & Supply-Chain
Protect operations with identity safeguards, device control, and threat monitoring
View the framework that guides DefenderSuite’s security and compliance solutions
Cybersecurity News
Insights and updates on threats, best practices, and regulatory changes affecting Australian businesses
Cyber Readiness Assessment
Complete a short assessment for a clear snapshot of your security maturity and next steps
Ransomware Reporting Template
Step-by-step templates to help your business meet the Cyber Security Act’s ransomware reporting requirements
FAQs
Find answers to common questions about DefenderSuite plans, security features, and compliance support
Complete Managed Cybersecurity, Compliance Built In.
DefenderSuite combines continuous threat monitoring, compliance management, and monthly reporting into a single managed plan — built for Australian businesses navigating the Essential Eight, DISP, PSPF, Government Contracts and cyber insurance requirements.